Beyond the Hype Unpacking the Lucrative Landscape of Blockchain Revenue Models
Sure, I can help you with that! Here's a soft article on "Blockchain Revenue Models," structured in two parts as you requested.
The term "blockchain" has, for years, been synonymous with the meteoric rise and sometimes dramatic falls of cryptocurrencies. Bitcoin, Ethereum, and their ilk captured the world's imagination, promising a financial revolution. Yet, beneath the surface of speculative trading and volatile market caps, a far more profound and sustainable transformation has been brewing. Blockchain technology, at its core, is a distributed, immutable ledger that offers unprecedented transparency, security, and efficiency. This fundamental innovation is not just about digital money; it's about reimagining how value is created, exchanged, and monetized across industries.
Moving beyond the initial hype, a sophisticated ecosystem of blockchain revenue models is emerging, demonstrating the technology's versatile applicability. These models are not simply extensions of traditional business strategies; they represent a paradigm shift, leveraging decentralization, tokenization, and network effects to unlock new avenues for profitability. Understanding these models is key to grasping the true potential of blockchain and its ability to reshape the digital economy.
One of the most foundational revenue streams, of course, stems from the very existence of cryptocurrencies. Transaction fees are an inherent part of most blockchain networks. Miners or validators who secure the network and process transactions are rewarded with these fees, which are paid by users initiating transactions. While these fees can fluctuate based on network congestion and the specific cryptocurrency, they represent a continuous income for those maintaining the blockchain's integrity. For public blockchains like Bitcoin and Ethereum, these fees are not just a cost of doing business; they are the economic incentive that drives network security. Without them, the decentralized infrastructure would simply cease to function.
Beyond these direct network fees, the concept of tokenization has opened a Pandora's Box of revenue-generating possibilities. Tokenization is the process of converting a right to an asset into a digital token on a blockchain. This can apply to virtually anything of value – real estate, art, intellectual property, commodities, or even fractional ownership of companies. By creating digital tokens, assets become more liquid, divisible, and easily transferable. For businesses, this translates into new revenue streams through:
Token Sales (ICOs, STOs, IEOs): Initial Coin Offerings (ICOs), Security Token Offerings (STOs), and Initial Exchange Offerings (IEOs) have been revolutionary ways for blockchain projects and startups to raise capital. While the regulatory landscape has evolved significantly since the ICO boom, these mechanisms, when compliant, allow projects to sell a portion of their future utility or equity in the form of tokens, generating immediate funds for development, marketing, and operations. This model is particularly attractive for early-stage ventures that might struggle to secure traditional venture capital. Primary and Secondary Token Sales: Once a project's token is launched, there can be ongoing opportunities for revenue. Projects can continue to sell tokens from their treasury to fund ongoing development or operations. Furthermore, secondary market trading of these tokens, facilitated by exchanges, creates liquidity and demand, indirectly benefiting the project through increased adoption and network effects, even if the project doesn't directly capture revenue from every trade. Utility Token Premiums: Many blockchain projects issue utility tokens that grant holders access to specific services, features, or discounts within their ecosystem. The perceived value and demand for these utility tokens can drive their price, creating a revenue stream for the project when they are initially sold or if the project retains a portion for future distribution. The more useful and integrated the token is within the ecosystem, the higher its perceived value and the greater the revenue potential.
The rise of Decentralized Applications (dApps) has introduced a wealth of new revenue models, mirroring and adapting traditional software monetization strategies to a decentralized environment. dApps are applications that run on a blockchain or peer-to-peer network, rather than a single server, making them resistant to censorship and downtime.
Transaction Fees within dApps: Similar to network transaction fees, dApps can implement their own internal fees for specific actions or services. For instance, a decentralized exchange (DEX) will typically charge a small fee on each trade. A decentralized gaming platform might charge a fee for in-game transactions or the creation of digital assets. These fees are often paid in the dApp's native token or a major cryptocurrency, providing a direct revenue stream for the dApp developers and operators. Subscription and Access Models: While a stark contrast to the typical "fee-for-service" model, some dApps are exploring subscription-based access to premium features or exclusive content. This is particularly relevant for dApps that offer ongoing services or data analysis. Users pay a recurring fee (often in cryptocurrency) to maintain access, providing a more predictable revenue stream. Decentralized Finance (DeFi) Yield Farming and Staking Rewards: The DeFi sector, built entirely on blockchain, has created entirely new financial instruments and revenue opportunities. Protocols often incentivize users to provide liquidity or stake their tokens to secure the network or facilitate trading. In return, users receive rewards, often in the form of newly minted tokens or a share of protocol fees. For the protocols themselves, these mechanisms are crucial for bootstrapping liquidity and network growth, and often, a portion of the generated rewards or fees can be allocated to the development team or treasury. This is a powerful example of how decentralization can align incentives and generate value for all participants. NFT Royalties and Creator Economies: Non-Fungible Tokens (NFTs) have revolutionized digital ownership, particularly in art, collectibles, and gaming. Beyond the initial sale of an NFT, smart contracts can be programmed to automatically pay a percentage of all future secondary sales back to the original creator. This has created a sustainable revenue model for artists and creators, allowing them to earn royalties on their work indefinitely. For platforms that facilitate NFT marketplaces, they can capture a percentage of these primary and secondary sales, alongside potential listing fees. This opens up a powerful avenue for creators to build a consistent income stream from their digital creations.
The shift towards Web3, the next iteration of the internet, is intrinsically tied to blockchain and is spawning further innovative revenue models. Web3 aims to be a decentralized, user-owned internet, where individuals have more control over their data and digital identities. This fundamentally changes the power dynamics and economic structures of online platforms.
Data Monetization and Ownership: In traditional Web2, companies monetize user data. In Web3, users can potentially own and monetize their own data. Blockchain-based identity solutions and decentralized data marketplaces allow individuals to grant permissioned access to their data to advertisers or researchers, receiving cryptocurrency in return. This flips the traditional advertising model on its head, empowering users and creating a direct revenue stream from their digital footprint. Decentralized Autonomous Organizations (DAOs) and Treasury Management: DAOs are organizations governed by smart contracts and community consensus, rather than a central authority. Their treasuries, often funded through token sales or revenue-generating activities, can be managed and invested through various blockchain-based strategies, including providing liquidity to DeFi protocols, investing in other Web3 projects, or funding community initiatives. The revenue generated by the DAO can then be distributed to token holders or reinvested. Platform Fees and Staking for Governance: Many Web3 platforms, akin to dApps, charge fees for their services. However, they often integrate a governance element where holding and staking the platform's native token grants users voting rights on important decisions. This encourages long-term investment in the platform's success and provides a clear incentive for users to participate. The fees collected can then be used for protocol development, marketing, or distributed to stakers and governance participants.
The underlying principle across many of these models is the concept of network effects. As more users join a blockchain network or dApp, its value and utility increase, attracting even more users. Revenue models that are designed to incentivize participation and growth, such as token distribution for liquidity provision or staking rewards, are particularly effective at harnessing these effects. The more participants there are, the more valuable the network becomes, leading to increased transaction volumes, greater demand for native tokens, and ultimately, higher revenue for the ecosystem as a whole. This symbiotic relationship is a cornerstone of the blockchain economy. The journey from cryptocurrency speculation to a robust ecosystem of sustainable blockchain revenue models is well underway, and the innovation continues to unfold at a breathtaking pace.
The decentralized nature of blockchain technology is not merely a technical curiosity; it's a fundamental enabler of novel revenue models that fundamentally challenge centralized intermediaries. By removing gatekeepers and fostering peer-to-peer interactions, blockchain allows for more direct value capture and distribution. This disintermediation is at the heart of many of the most promising blockchain revenue streams.
Consider the realm of enterprise blockchain solutions. While much of the public discourse focuses on cryptocurrencies and public ledgers, private and permissioned blockchains are quietly revolutionizing business operations. Companies are leveraging blockchain for supply chain management, identity verification, secure data sharing, and process automation. The revenue models here are often more traditional, yet enhanced by blockchain's capabilities:
SaaS (Software as a Service) for Blockchain Platforms: Companies offering blockchain-as-a-service (BaaS) platforms provide businesses with the infrastructure and tools to build and deploy their own blockchain solutions without needing deep technical expertise. Revenue is generated through recurring subscription fees, tiered service levels, and potentially, usage-based charges for transaction processing or data storage. Think of it as renting access to a powerful, secure, and distributed database. Consulting and Implementation Services: The complexity of integrating blockchain technology into existing business processes necessitates expert guidance. Companies specializing in blockchain consulting can command significant fees for designing, developing, and implementing bespoke blockchain solutions for enterprises. This includes everything from smart contract auditing to full-scale distributed ledger network deployment. Licensing of Blockchain Technology: For companies that have developed proprietary blockchain protocols or innovative smart contract frameworks, licensing their technology to other businesses can be a lucrative revenue stream. This allows them to monetize their intellectual property and expertise without necessarily building out the entire operational infrastructure themselves. Data Monetization and Marketplaces: Blockchain can create secure and transparent marketplaces for data. Enterprises can utilize blockchain to track and verify the provenance of data, ensuring its integrity. They can then monetize access to this verified data, either directly through sales or by enabling data-sharing agreements with other businesses, all managed and secured by blockchain. For example, a consortium of pharmaceutical companies could use a blockchain to share anonymized patient data for research purposes, with each participant earning revenue based on their contribution and usage.
The advent of tokenized economies extends beyond simple asset tokenization into complex ecosystems where tokens themselves become the medium of exchange and value accrual.
Staking and Validator Rewards: As mentioned earlier, public blockchains require participants (miners or validators) to secure the network. These participants invest capital (often in the form of the native cryptocurrency) and are rewarded with newly minted tokens and transaction fees. This model incentivizes the growth and security of the network, creating a perpetual revenue stream for those who contribute computational power or capital. For nascent blockchains, this is a crucial mechanism to bootstrap security and decentralization. Liquidity Provision and Yield Farming Incentives: In DeFi, providing liquidity to decentralized exchanges (DEXs) or lending protocols is essential for their operation. Protocols often offer attractive yield farming rewards – additional tokens distributed to liquidity providers – to incentivize them to lock up their assets. While users earn these rewards, the underlying protocols themselves often capture a portion of trading fees or interest generated, which can then be used for further development, marketing, or distributed to governance token holders. This creates a dynamic where participation directly fuels the protocol's revenue and growth. Decentralized Advertising and Data Marketplaces: Imagine an internet where you are directly compensated for viewing ads or for granting access to your data. Blockchain-powered advertising platforms are emerging that allow users to opt-in to seeing advertisements and receive micro-payments in cryptocurrency for their attention. Similarly, decentralized data marketplaces empower individuals to sell their data directly to businesses, bypassing traditional data brokers and capturing the full value of their information. The platform facilitating these transactions takes a small fee, creating a revenue stream that aligns with user interests.
The concept of "play-to-earn" (P2E) gaming has exploded in popularity, demonstrating a powerful new revenue model rooted in digital ownership and active participation. In P2E games, players can earn cryptocurrency or NFTs by completing tasks, winning battles, or contributing to the game's economy.
In-Game Asset Sales (NFTs): Players can earn or purchase unique in-game items, characters, or land as NFTs. These assets can then be traded with other players on marketplaces, either within the game or on external platforms. The original game developers often take a percentage of these secondary market sales, creating a continuous revenue stream that is directly tied to the engagement and economic activity of their player base. Game Development and Royalties: For game developers, P2E models offer a direct way to monetize their creations. Beyond initial game sales or in-app purchases (which can also be tokenized), the ongoing trading of in-game assets creates a royalty-based revenue model. The more popular and engaging the game, the more active the player-driven economy, and the higher the potential for sustained revenue for the developers. Ecosystem Development and Tokenomics: Successful P2E games often have intricate tokenomics designed to encourage long-term player retention and economic sustainability. This can involve multiple in-game currencies, staking mechanisms for in-game advantages, or governance tokens that give players a say in the game's future. The revenue generated can be used to further develop the game, fund esports events, or even create new complementary games within the same universe, building a cohesive and profitable blockchain gaming ecosystem.
Looking ahead, the convergence of AI, IoT, and blockchain is poised to unlock even more sophisticated revenue models. Imagine smart devices autonomously negotiating and executing transactions on a blockchain, earning revenue for their owners or the manufacturers.
Decentralized Cloud Computing and Storage: Projects are emerging that allow individuals and businesses to rent out their unused computing power or storage space, creating a decentralized marketplace for these resources. Users earn cryptocurrency for contributing, while others pay for access, all managed securely and transparently by blockchain. Decentralized Identity and Reputation Systems: As individuals build verifiable digital identities and reputations on the blockchain, these attributes themselves can become valuable. Users could potentially monetize their reputation by granting verified access to services or platforms, or by demonstrating expertise. The platforms that facilitate the creation and verification of these identities could, in turn, generate revenue through premium services or partnerships. Carbon Credits and Environmental Markets: Blockchain is being used to create transparent and immutable marketplaces for carbon credits and other environmental assets. This can lead to more efficient and trustworthy trading, potentially creating new revenue streams for entities that invest in sustainable practices and generate verifiable environmental benefits.
The success of these revenue models hinges on several key factors: strong community engagement, robust tokenomics, regulatory clarity, and demonstrable utility. The initial speculative frenzy around some blockchain applications has given way to a more mature understanding of how to build sustainable, value-generating businesses. The future of blockchain revenue is not just about selling digital coins; it's about building resilient, user-centric economies where value is created, distributed, and captured in entirely new ways, driven by the fundamental principles of transparency, security, and decentralization. The ongoing evolution of these models promises to reshape industries and redefine how we think about profit and value in the digital age.
Introduction to Quantum Protection Wallets
In an era where digital footprints are ubiquitous, the need for robust security solutions has never been greater. Enter Quantum Protection Wallets—a groundbreaking innovation designed to safeguard your digital assets with the power of quantum technology. At their core, these wallets utilize quantum-safe encryption to ensure that your data remains unbreachable by even the most advanced cyber threats.
The Science Behind Quantum Encryption
Quantum encryption leverages the principles of quantum mechanics to create encryption methods that are theoretically immune to hacking. Unlike traditional encryption, which relies on complex mathematical algorithms, quantum encryption uses quantum bits or qubits. These qubits exist in a state of superposition, meaning they can be both 0 and 1 simultaneously. When measured, they collapse into a definite state, but only one at a time. This fundamental property allows quantum encryption to generate keys that are virtually impossible to crack.
How Quantum Protection Wallets Work
Quantum Protection Wallets combine the strengths of quantum encryption with the efficiency of blockchain technology. They are designed to protect digital currencies, personal data, and sensitive information from cyber threats. Here’s how they work:
Key Generation: Quantum encryption generates keys that are unique and secure. These keys are generated using quantum random number generators, ensuring that each key is truly random and secure.
Encryption: Data is encrypted using these quantum keys, ensuring that even if intercepted, it remains unreadable without the correct decryption key.
Storage: The quantum keys are stored in secure quantum vaults, which are protected by quantum-safe algorithms. These vaults are resistant to traditional hacking methods and quantum attacks alike.
Transactions: When a transaction is initiated, the Quantum Protection Wallet uses the quantum keys to encrypt the transaction details, ensuring that they remain secure throughout the process.
Real-World Applications
Quantum Protection Wallets are not just a theoretical concept; they are already being used in various real-world applications. Here are some of the areas where these wallets are making a significant impact:
Finance: Banks and financial institutions are adopting Quantum Protection Wallets to secure transactions and protect against cyber fraud. The encryption used in these wallets ensures that sensitive financial data remains private and secure.
Healthcare: In the healthcare sector, Quantum Protection Wallets are used to safeguard patient records and personal health information. This ensures that medical data remains confidential and protected from unauthorized access.
Government: Governments are leveraging Quantum Protection Wallets to secure sensitive information and communications. These wallets help protect national security and ensure that critical data remains safe from cyber threats.
Future of Digital Security
The future of digital security looks promising with the advent of Quantum Protection Wallets. As quantum computing technology continues to evolve, these wallets will become even more sophisticated and powerful. Here’s what to expect:
Enhanced Security: With advancements in quantum technology, the encryption methods used in Quantum Protection Wallets will become even more secure, offering unparalleled protection against future cyber threats.
Wider Adoption: As awareness of the importance of quantum-safe encryption grows, more industries and individuals will adopt Quantum Protection Wallets. This will lead to a significant reduction in cyber attacks and data breaches.
Regulatory Compliance: Governments and regulatory bodies are likely to mandate the use of quantum-safe encryption in various sectors. Quantum Protection Wallets will play a crucial role in ensuring compliance with these regulations.
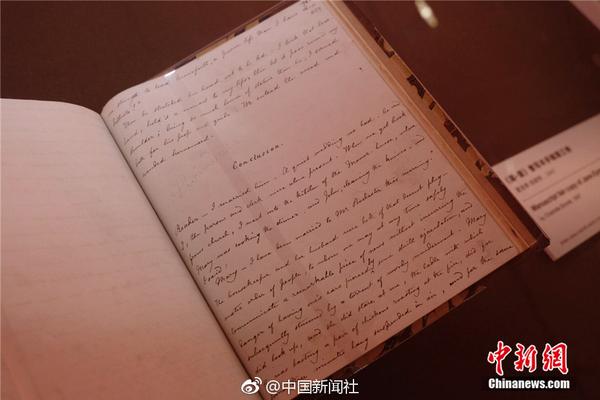
Conclusion
Quantum Protection Wallets represent a significant leap forward in digital security. By harnessing the power of quantum encryption, these wallets offer a robust defense against cyber threats, ensuring that your digital assets remain safe and secure. As we move further into the quantum era, these wallets will become an essential tool for anyone looking to protect their data in a digital world.
Deep Dive into Quantum Protection Wallets
In the previous section, we explored the basics of Quantum Protection Wallets and their real-world applications. Now, let's delve deeper into the technology behind these wallets, their benefits, and how they compare to traditional security methods.
The Mechanics of Quantum Encryption
Quantum encryption, also known as post-quantum cryptography, is a type of encryption that uses quantum mechanics to create cryptographic keys that are secure against both classical and quantum computers. Unlike traditional encryption methods that rely on the difficulty of mathematical problems (like factoring large numbers or solving discrete logarithms), quantum encryption leverages the unique properties of quantum mechanics.
Key Concepts in Quantum Encryption
Quantum Key Distribution (QKD): This is a method for securely sharing encryption keys between two parties. QKD uses the principles of quantum mechanics to ensure that any attempt to eavesdrop on the key will be detected. This is because measuring a quantum state (like a qubit) alters it, making any interception evident.
Superposition and Entanglement: Qubits can exist in multiple states simultaneously (superposition) and can be entangled, meaning the state of one qubit can depend on the state of another, no matter the distance between them. These properties make quantum keys incredibly secure.
Advantages of Quantum Protection Wallets
Quantum Protection Wallets offer several advantages over traditional security methods:
Unbreakable Security: Quantum encryption is theoretically immune to hacking, making it impossible for even the most powerful quantum computers to crack the encryption.
Future-Proof: As quantum computing technology advances, traditional encryption methods will become vulnerable. Quantum Protection Wallets are designed to be future-proof, ensuring long-term security.
Enhanced Privacy: These wallets provide robust privacy protection, safeguarding sensitive information from unauthorized access and ensuring that personal data remains confidential.
Efficient and Fast: Quantum encryption methods are not only secure but also efficient, allowing for faster and more secure transactions compared to traditional encryption methods.
Comparing Quantum Protection Wallets to Traditional Security
While traditional security methods have been effective in the past, they are no longer sufficient in the face of evolving cyber threats. Here’s how Quantum Protection Wallets compare to traditional security:
Vulnerability to Quantum Computers: Traditional encryption methods, such as RSA and ECC, will be vulnerable to quantum computers that can solve complex mathematical problems at unprecedented speeds. Quantum Protection Wallets, on the other hand, are designed to be secure against quantum attacks.
Ease of Use: Quantum Protection Wallets integrate seamlessly with existing systems, offering a user-friendly interface that makes it easy to adopt without significant changes to current workflows.
Cost-Effective: While the initial investment in quantum technology may be high, the long-term benefits of enhanced security and reduced risk of data breaches make Quantum Protection Wallets cost-effective in the long run.
Implementation and Integration
Implementing Quantum Protection Wallets involves several key steps to ensure a smooth transition from traditional security methods to quantum-safe encryption:
Assessment: Conduct a thorough assessment of current security measures and identify areas that require quantum-safe encryption.
Selection: Choose the right Quantum Protection Wallet that meets your specific needs in terms of security, ease of use, and integration with existing systems.
Deployment: Implement the Quantum Protection Wallet across your network, ensuring that all users are trained and familiar with the new system.
Monitoring: Continuously monitor the performance of the Quantum Protection Wallet to ensure it is functioning optimally and to address any emerging threats.
Case Studies and Success Stories
Several organizations have already adopted Quantum Protection Wallets and have seen significant improvements in their security posture. Here are a few case studies:
Case Study 1: Global Financial Institution
A major global financial institution implemented Quantum Protection Wallets to secure its digital transactions. The institution reported a 90% reduction in cyber attacks and a significant improvement in the security of its sensitive financial data. The seamless integration of quantum encryption ensured that the institution remained compliant with international security standards.
Case Study 2: Healthcare Provider
A large healthcare provider adopted Quantum Protection Wallets to safeguard patient records. The implementation led to a notable increase in patient trust and a reduction in data breaches. The enhanced security measures provided peace of mind, knowing that personal health information was protected by cutting-edge technology.
Case Study 3: Government Agency
A government agency implemented Quantum Protection Wallets to secure sensitive communications and data. The agency experienced a significant decrease in unauthorized access attempts and improved compliance with national security regulations. The advanced security features of the Quantum Protection Wallet ensured that critical data remained protected.
The Role of Blockchain Technology
Blockchain technology plays a crucial role in the functionality and efficiency of Quantum Protection Wallets. By combining quantum encryption with blockchain, these wallets offer a secure and transparent way to manage digital assets. Here’s how blockchain enhances the capabilities of Quantum Protection Wallets:
Transparency: Blockchain provides a transparent ledger of all transactions, ensuring that every action is recorded and traceable. This transparency helps in detecting and preventing fraudulent activities.
Immutability: Once a transaction is recorded on a blockchain, it cannot be altered or deleted. This immutability ensures that transaction records remain secure and tamper-proof.
量子保护钱包的作用
数据保护: 量子保护钱包通过量子加密技术,确保数据在传输和存储过程中不被窃取和篡改。这对于敏感信息,如个人隐私、金融数据和政府机密,至关重要。
身份认证: 量子保护钱包可以提供更安全的身份认证方法。通过量子密钥分发(QKD),用户可以获得独特的加密密钥,确保身份信息在认证过程中的安全。
交易安全: 在区块链和加密货币领域,量子保护钱包确保交易的安全性和完整性。通过量子加密技术,防止交易信息被篡改或窃取。
未来趋势
普及和标准化: 随着量子计算技术的发展,量子保护钱包将逐渐普及。国际标准化组织可能会制定量子安全标准,以确保不同系统之间的兼容性和安全性。
跨行业应用: 量子保护钱包不仅限于金融领域,还将扩展到医疗、教育、政府等多个行业。例如,在医疗领域,量子保护钱包可以确保患者隐私数据的安全,在教育领域,可以保护学生信息和学术研究数据。
集成人工智能: 未来的量子保护钱包可能会与人工智能(AI)技术结合,通过智能分析和预测,进一步提升安全性。例如,AI可以实时监控网络活动,识别异常行为并自动采取保护措施。
量子互联网: 随着量子互联网的发展,量子保护钱包将在量子通信网络中发挥重要作用。量子互联网将通过量子密钥分发和量子加密技术,提供无法破解的通信保障。
技术挑战和解决方案
尽管量子保护钱包具有巨大的潜力,但仍面临一些技术挑战:
量子计算机的普及: 目前,商用量子计算机还不普及,但随着技术进步,这一挑战将逐步被克服。研究机构和企业正在加快量子计算机的开发和应用。
基础设施建设: 建设支持量子加密和量子密钥分发的基础设施是一个长期挑战。需要投资于高性能量子计算设备和相关通信基础设施。
标准和互操作性: 缺乏统一的标准可能导致不同系统之间的互操作性问题。国际标准化组织和行业协会正在努力制定统一的量子安全标准。
结论
量子保护钱包代表了未来数字安全的前沿技术,其强大的加密能力和前瞻性的安全特性,将在多个领域发挥重要作用。尽管目前面临一些挑战,但随着技术的不断进步和标准的逐步完善,量子保护钱包将为我们的数字生活带来更高的安全保障。
Beyond the Hype Mastering the Art of Earning Smarter in the Crypto Frontier
Decoding the Digital Gold Rush Where Smart Money Flows in the Blockchain Era